UCCS Cybersecurity Distinguished Lecture Series
UCCS Cybersecurity Distinguished Lecture Series
-
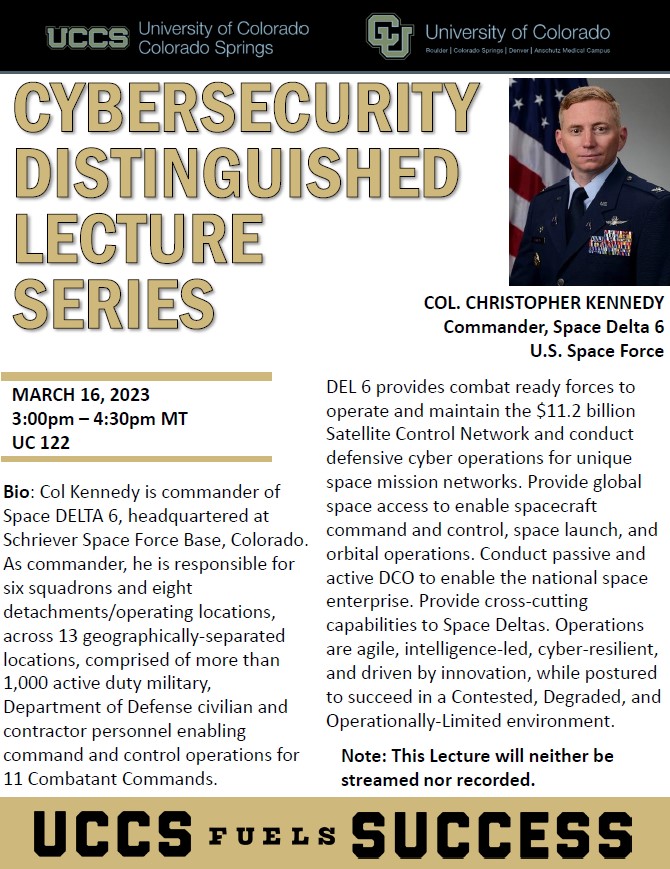
COL. Christopher Kennedy Commander, Space Delta 6 U.S. Space Force
-
Preparing for Exponential Growth in Space and Cyber
-
On Deploying Secure Computation Protocols in Daily Business Applications
Speaker: Dr. Moti Yung
When and Where: May 13, 2022 at 11am-1pm MT; Virtual
Abstract: The area of Secure Computation Protocols is the third generation of modern cryptography, where Symmetric Key Encryption was the first generation, and Public Key Cryptography was the second one. The area started with the Mental Poker protocol in the late 70s, has been a theoretical research area for 40 years, with more applied protocols in recent years. In this talk I will cover an effort that led to the first cryptographic protocols working routinely in business applications, employing secure computation (rather than the typical secure communication). I will argue why our time is technologically the right setting for adopting secure computation, and how we approached the deployment. The talk will explain the why and how, and also some of the technical developments that were needed to design the protocol to actual business needs and performance requirements, allowing two companies to compute on shared data results that are critical to business, while keeping the inputs otherwise mutually private.
Short bio: Moti Yung is a Security and Privacy Research Scientist with Google. He got his PhD from Columbia University in 1988. Previously, he was with IBM Research, Certco, RSA Laboratories, and Snap. He has also been an adjunct senior research faculty at Columbia, where he has co-advised and worked with PhD students. His contributions to research and development treat science and technology holistically: from the theoretical mathematical foundations, via conceptual mechanisms, to applied cryptography, and to participation in developing actual industrial products. Yung is a Fellow of the IEEE, the Association for Computing Machinery (ACM), the International Association for Cryptologic Research (IACR), and the European Association for Theoretical Computer Science (EATCS). In 2010 he gave the IACR Distinguished Lecture. He is the recipient of the 2014 ACM SIGSAC Outstanding Innovation award, and the 2014 ESORICS (European Symposium on Research in Computer Security) Outstanding Research Award. In 2018 he received the IEEE-CS W. Wallace McDowell Award. In 2020 he received the test-of-time award for a paper predicting ransomware, co-authored in 1996 in IEEE’s Symposium on Security and Privacy; also in 2020 he received the IACR’s PKC conference test-of-time award for a paper he co-authored in 1998. In 2021 he received the IEEE-CS Computer Pioneer Award.
-
Challenges in Cyber Risk Analysis of Critical Infrastructures
Speaker: Professor David M. Nicol (UIUC)
When and Where: April 8, 2022 at 11am-1pm MT; Virtual
Abstract: Critical infrastructures such as the power grid, oil and gas production/transportation, water systems, and transportation are now controlled by networks of computer and communication devices. This architecture creates opportunities for adversaries to remotely impact the operations of those infrastructures through the cyber-network, causing loss of service, damage to equipment, loss of confidence in the company running the infrastructure, and so on. Devices in the computing/communication network may have vulnerabilities which, depending on access, permit an adversary to take control of them, and/or inhibit their abilities to provide service. This talk considers challenges related to defining the risk to the critical infrastructure induced by cyber-access, mathematical assessment of that risk, and ways of reducing the risk while minimizing the negative impact that risk reduction has on provisioning of essential services.
Bio: David M. Nicol holds the Herman M. Dieckamp Endowed Chair in Engineering at the University of Illinois at Urbana Champaign. He is Director of the Information Trust Institute there, and is a member of the Department of Electrical and Computer Engineering. He is Principal Investigator on three large centers focused on resilience, one funded by the Department of Energy (CREDC, www.cred-c.org), one funded by the Department of Homeland Security (CIRI, ciri.illinois.edu) , and a new NSF I/UCRC CITES (Center for Infrastructure Trust in Energy Systems). He holds a B.A. in mathematics from Carleton College, and Ph.D. in computer science from the University of Virginia. He is the inaugural recipient of the ACM SIGSIM Distinguish Contributions Award, and has been elected Fellow of the IEEE and Fellow of the ACM.
-
CACTI: Captcha Avoidance via Client-side TEE Integration
Speaker: Professor Gene Tsudik (UCI)
When and Where: March 18, 2022 at 11am-1pm MT @UC 122 on Zoom
Abstract: Preventing abuse of web services by bots is an increasingly important problem, as abusive activities grow in both volume and variety. CAPTCHAs are the most common way for thwarting bot activities. However, they are often ineffective against bots and frustrating for humans. In addition, some recent CAPTCHA techniques diminish user privacy. Meanwhile, client-side Trusted Execution Environments (TEEs) are becoming increasingly widespread (notably, ARM TrustZone and Intel SGX), allowing establishment of trust in a small part (trust anchor or TCB) of client-side hardware. This prompts the question: can a TEE help reduce (or remove entirely) user burden of solving CAPTCHAs?
In this work, we design CACTI: CAPTCHA Avoidance via Client-side TEE Integration. Using client-side TEEs, CACTI allows legitimate clients to generate unforgeable rate-proofs demonstrating how frequently they have performed specific actions. These rate-proofs can be sent to web servers in lieu of solving CAPTCHAs. CACTI provides strong client privacy guarantees, since the information is only sent to the visited website and authenticated using a group signature scheme. Our evaluations show that overall latency of generating and verifying a CACTI rate-proof is less than 0:25 sec, while CACTI bandwidth overhead is over 98% lower than that of current CAPTCHA systems.
Bio: Gene Tsudik is a Distinguished Professor of Computer Science at the University of California, Irvine (UCI). He obtained his PhD in Computer Science from USC in 1991. Before coming to UCI in 2000, he was at the IBM Zurich Research Laboratory (1991-1996) and USC/ISI (1996-2000). His research interests include many topics in security, privacy and applied cryptography. Gene Tsudik is a Fulbright Scholar, Fulbright Specialist (thrice), a fellow of ACM, IEEE, AAAS, IFIP and a foreign member of Academia Europaea. From 2009 to 2015 he served as Editor-in-Chief of ACM Transactions on Information and Systems Security (TISSEC, renamed TOPS in 2016). Gene was the recipient of 2017 ACM SIGSAC Outstanding Contribution Award. He is also the author of the first crypto-poem published as a refereed paper.
-
Security of 4G and 5G Cellular Networks
Speaker: Professor Elisa Bertino (Purdue)
When and Where: February 11th, 2022, 11am – 1pm MT on Zoom
Abstract: As the world moves to 4G & 5G cellular networks, security & privacy are of paramount importance, & new tools are needed to ensure them. For ex., LTEInspector is a model-based testing approach combining a symbolic model checker & cryptographic protocol verifier in the symbolic attacker model. Using it, researchers have uncovered 10 new attacks along with 9 prior attacks, categorized into 3 abstract classes (i.e., security, user privacy, and disruption of service) in 3 procedures of 4G LTE. Notable findings is the authentication relay attack that enables an adversary to spoof the location of a legitimate user to the core network without possessing appropriate credentials. To ensure the exposed attacks pose real threats & are indeed realizable in practice, 8 of 10 new attacks have been validated, & their accompanying adversarial assumptions have been put through a real testbed. Ongoing work in addressing some of those vulnerabilities points the way toward further research.
Bio: Elisa Bertino is professor of Computer Science at Purdue University. Prior to joining Purdue, she was a professor and department head at the Department of Computer Science and Communication of the University of Milan. She has been a visiting researcher at the IBM Research Laboratory in San Jose (now Almaden), at the Microelectronics and Computer Technology Corporation, at Rutgers University, at Telcordia Technologies. She has also held visiting professor positions at the Singapore National University and the Singapore Management University. Her main research interests include security, privacy, database systems, distributed systems, and sensor networks. Her recent research focuses on cybersecurity and privacy of cellular networks and IoT systems, and on edge analytics for cybersecurity. Elisa Bertino is a Fellow member of IEEE, ACM, and AAAS. She received the 2002 IEEE Computer Society Technical Achievement Award for “For outstanding contributions to database systems and database security and advanced data management systems”, the 2005 IEEE Computer Society Tsutomu Kanai Award for “Pioneering and innovative research contributions to secure distributed systems”, and the 2019-2020 ACM Athena Lecturer Award.
-
VEST: An Early Warning System for Future Cyber-Attacks
Speaker: V.S. Subrahmanian (Northwestern)
When and Where: Dec 10, 2021 11:00 AM MT on Zoom
Abstract: We consider the problem of predicting cyber-attacks based on known Common Vulnerability & Exposure (CVE) numbers. Given a CVE, we wish to answer 3 questions: (i) Will the CVE be exploited by malicious hackers? (ii) If so, when? (iii) How severe will the attack be? The answers to these questions are critical for almost all companies with significant software/hardware investments, for manufacturers of those software/hardware components, and for governments of the nations involved. In this talk, I will primarily focus on when a vulnerability will be exploited. Using a 23-month dataset gleaned from 5 sources, I will present a novel family of CAT (CVE-Author-Tweet) graphs. Each CAT graph has a massive associated system of recursive equations whose solution yields ``popularity scores’’ for the CVE-Author-Tweet nodes in the graph. Using these scores for different CAT graphs, we show a model that can predict when a vulnerability will be exploited – and we will use real world case studies to illustrate the efficacy of the approach. The talk will briefly describe progress on problems (i) and (iii) as well, and will describe a research agenda going forward that uses the predictions generated to better secure an enterprise. I will conclude with a brief outline of policy questions resulting from our work.
Speaker Bio: V.S. Subrahmanian is the Walter P. Murphy Professor of Computer Science and Buffett Faculty Fellow in the Buffett Institute for Global Affairs at Northwestern University. He was previously the Dartmouth College Distinguished Professor in Cybersecurity, Technology, and Society and Director of the Institute for Security, Technology, and Society at Dartmouth. Prior to that, he served as a Professor of Computer Science at the University of Maryland from 1989-2017 where he also served for 6+ years as Director of the University of Maryland's Institute for Advanced Computer Studies. Prof. Subrahmanian is an expert on big data analytics including methods to analyze text/geospatial/relational/social network data, learn behavioral models from the data, forecast actions, and influence behaviors with applications to cybersecurity and counter-terrorism. He has written six books, edited ten, and published over 300 refereed articles. He is a Fellow of the American Association for the Advancement of Science and the Association for the Advancement of Artificial Intelligence and has received numerous other honors and awards. His work has been featured in numerous outlets such as the Baltimore Sun, the Economist, Science, Nature, the Washington Post, American Public Media and more. He serves on the editorial boards of numerous journals including Science, and currently serves on the Board of Directors of SentiMetrix, Inc. and on the Research Advisory Board of Tata Consultancy Services. He previously served on the Board of Directors of the Development Gateway Foundation (set up by the World Bank), DARPA's Executive Advisory Council on Advanced Logistics and as an ad-hoc member of the US Air Force Science Advisory Board.
-
Tackling Credential Abuse Together
Speaker: Professor Michael Reiter (Duke)
Where and when: Nov. 12, 2021 at 1-2pm MT on Zoom
Abstract: Despite long-ago predictions (e.g., see Bill Gates, 2004) that other user-authentication technologies would replace passwords, passwords remain not only pervasive but have flourished as the dominant form of account protection, especially at websites such as retailers that require a low-friction user experience. This talk will describe our research on methods to tackle three key ingredients of account takeovers for password-protected accounts today: (i) site database breaches, which is the largest source of stolen passwords for internet sites; (ii) the tendency of users to reuse the same or similar passwords across sites; and (iii) credential stuffing, in which attackers submit breached credentials for one site in login attempts for the same accounts at another. A central theme of our research is that these factors are most effectively addressed by coordinating across websites, in contrast to today's practice of each site defending alone. We describe algorithms to drive this coordination, demonstrate the efficacy and security of our proposals through conservative analyses, and demonstrate the scalability of our designs through working implementations. This research was performed jointly with Ke Coby Wang.
Bio: Michael Reiter is a James B. Duke Distinguished Professor in the Departments of Computer Science and Electrical & Computer Engineering at Duke University, which he joined in January 2021 following previous positions in industry (culminating as Director of Secure Systems Research at Bell Labs, Lucent) and academia (Professor of CS and ECE at Carnegie Mellon, and Distinguished Professor of CS at UNC-Chapel Hill). His technical contributions lie primarily in computer security and distributed computing, and include several that have seen widespread adoption. He was named an ACM Fellow in 2008, an IEEE Fellow in 2014, and winner of the ACM SIGSAC Outstanding Contributions Award in 2016.